Following the U.S. government sanctions against the Philippines-based tech firm Funnull Technology Inc. (or Funnull for short) for its role in large-scale online scams, new research from WhoisXML API shows that Funnull’s infrastructure is significantly larger, older, and more distributed than previously disclosed.
The FBI’s May 2025 Flash Report detailed Funnull’s role as an infrastructure provider for crypto scams and so-called pig-butchering scams, documenting over 332,000 unique domains either directly attributed to Funnull or associated with this infrastructure. The U.S. Treasury has attributed roughly $200 million in victim financial losses to those scam campaigns.
WhoisXML API’s latest analysis has uncovered more than 100,000 additional domains associated with the same infrastructure, expanding the timeline and technical scope of Funnull’s operations. Just like the ones listed by the FBI, most of the newly identified domains are also so-called DGAs – domains generated algorithmically, with domain names consisting mostly of numbers.
While the FBI’s dataset focused on recent activity in 2023-2025, WhoisXML API’s researchers traced domain registrations linked to Funnull back to 2020, suggesting the scam network has been active, or in preparation, for at least five years.
The group’s use of bulk registration patterns and their reliance on algorithmic domain name generation allowed researchers to cluster domains by timing and volume, revealing coordinated infrastructure activity designed to operate at scale.
WhoisXML API’s data shows a noticeable spike in domain registrations in late 2024, consistent with the FBI’s timeline, reinforcing the assumption of an accelerated campaign before the sanctions hit.
Distributed Infrastructure Built for Evasion
The infrastructure used by Funnull isn’t just large—it’s intentionally scattered. WhoisXML API’s researchers have identified that the scam-related infrastructure spans domain names across more than 400 top-level domains (TLDs)—up from the 240+ cited in the FBI report.
On the hosting side, domains resolved to IPs tied to at least 100 different ISPs, including major players like Cloudflare, Amazon, and Spartan Host. “The crypto-scam infrastructure is truly gigantic and seems to be heavily distributed across many TLDs and ISPs,” said Alexandre François, Director at WhoisXML API. “The main reason for this distribution is probably to make it harder to detect and take down, as well as more evasive.”
A prior Silent Push analysis had marked Amazon as the top host for Funnull-linked hostnames, with about 40% of domains connected to it. However, WhoisXML API’s findings show a broader distribution across additional providers, with Cloudie now accounting for the majority (65.1%) of infrastructure use, followed by Amazon and BGP Network Limited.
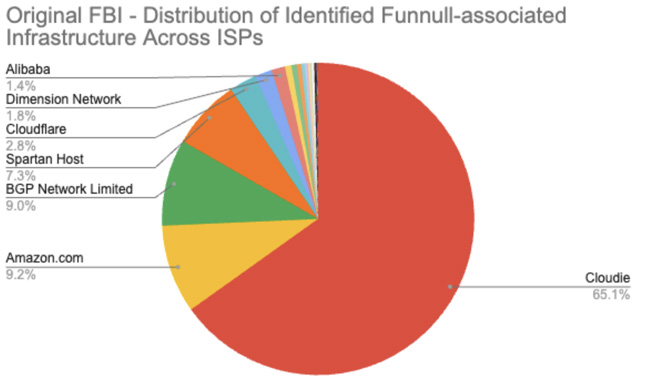
Figure 1. Distribution of the domains reported by the FBI across ISPs. Illustration by WhoisXML API
The distribution of the infrastructure across different TLDs and ISPs didn’t remain static over the years. A trend that WhoisXML API’s researchers noticed was a gradual move away from .com domains. Although .com remained dominant throughout 2023, registrations in 2025 increasingly shifted toward cheaper, less regulated TLDs like .top. The researchers believe this isn’t just about cost — .top domains, while inexpensive, are not the cheapest available. Instead, scammers may be weighing registrar responsiveness, enforcement policies, and perceived risk of detection.
According to WhoisXML API’s data, the majority of the IP addresses to which the domains resolved seem to be located in the U.S. or in Hong Kong. This correlates with previous findings that suggested that Funnull used to purchase IP addresses in the U.S. and then use them to host malicious infrastructure.
However, the geographical distribution isn’t limited to the two countries above, as some of the discovered IP addresses are based in other countries, such as Philippines, Malaysia, Spain, Cambodia, China, Iceland, and others.
The Challenges of Dealing with Distributed Infrastructure
Despite the enormous scale, the infrastructure seems to have been relatively inexpensive to operate as the $200 million in estimated earnings dwarfs the likely costs of bulk domain purchases. Many domains were registered for one year and never renewed, allowing operators to cycle through them at low cost. Domain registrars often offer new domains at significantly lower costs than what they charge for renewing existing ones.
Among domains registered between 2020 and 2023, WhoisXML API’s research indicates that fewer than 40% have retrievable WHOIS records today, suggesting the rest have been dropped or taken down.
This model — burner domains at industrial scale — demonstrates how cybercriminals maximize return on minimal investment, undermining defenders who rely on historical ownership data and registrant transparency.
Funnull’s infrastructure highlights how cybercriminals now operate like cloud-native organizations, optimizing for scale, distribution, and obfuscation. The shift away from predictable patterns—like reliance on a single TLD or hosting provider—makes traditional detection strategies harder to apply.
June 13, 2025However, it remains possible to identify even such dispersed domains using clustering techniques based on identifying domains registered in bulk and using registration timestamps and DNS data such as registrar and domain name server information to validate the findings.
