Latest News & Insights
VIEW ALL
Trusting Cheap SSL Certificate Providers when Budget is Low
You have a web presence. You have motives to succeed. Highly secured SSL certificates are expensive and you don’t need one of those, anyway. This…
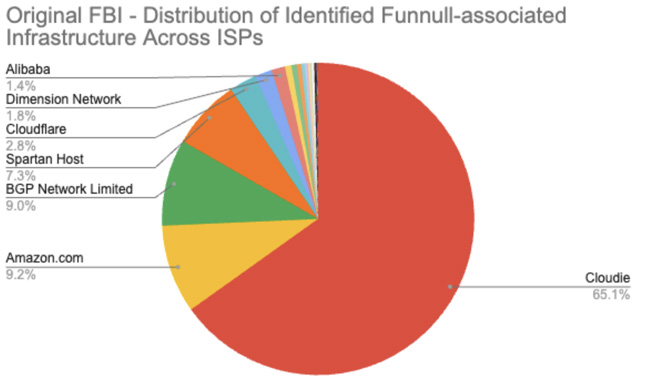
Funnull Scam Infrastructure Revealed to Be 100,000 Domains Larger and Older Than Previously Reported
Following the U.S. government sanctions against the Philippines-based tech firm Funnull Technology Inc. (or Funnull for short) for its role in large-scale online scams, new…

Best Laptop for Cybersecurity: Top Picks for Ethical Hackers & Security Professionals
Selecting the right Laptop For Cybersecurity is one of the most critical decisions for cybersecurity professionals. Whether you are a CISO, penetration tester, ethical hacker,…

CybersecurityWebinars.com: Your Gateway to Essential InfoSec Knowledge
Cybersecurity Webinars (CSW) is excited to announce the launch of its new platform, offering a comprehensive resource for cybersecurity professionals. This user-friendly website provides free…

Webinar: Managing Without Governing? Why Your Organization Needs a Management System to Govern Your Information Resilience Program
Most organizations have some kind of processes established for their day-to-day cyber security program, but most are missing the fact that while cyber security is…
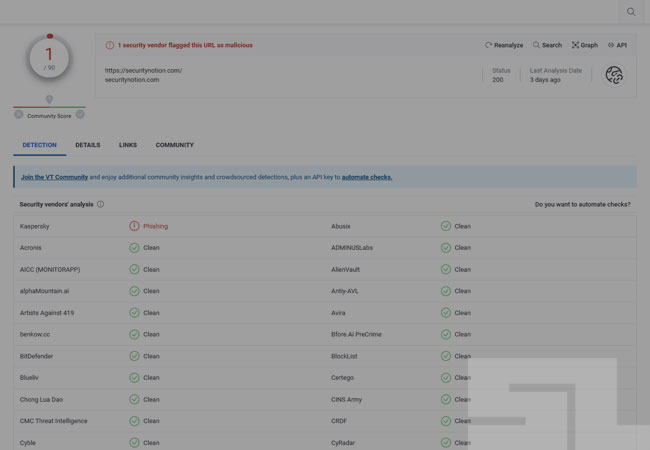
How to Remove False Positive URL (VirusTotal)
VirusTotal is a security platform where you can analyze suspicious files, websites, and URLs that may be malicious. When you submit a file or a…

Unmasking the Dark Art of Social Engineering: Exploring Lesser-Known Tactics
Social engineering remains a common tool in cybercriminals’ arsenal in the rapidly evolving landscape of attack vectors for users and organizations. While phishing attacks have…

The Three Best Defenses You Can Deploy
Every computer defender is inundated with over a hundred cybersecurity controls they are supposed to deploy to make their environment at reduced risk of cyber…

Artificial Intelligence and the Future of the Human Race
Some scientists are saying that AI will save the world. If this claim is valid, the main question is, at what cost? In 2023, 42%…